C Obfuscation Techniques
The quality of an obfuscation method is determined by the combination of its potency resilience stealth and cost. Short and meaningless identifiers.

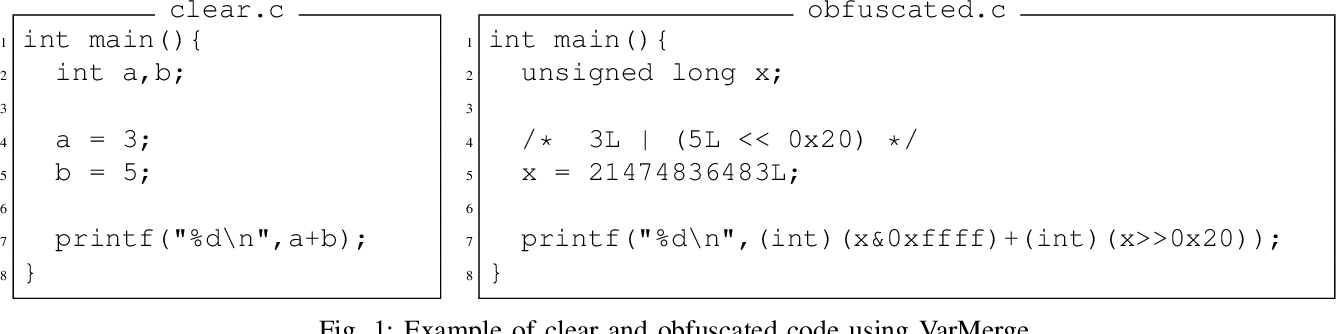
Example Of Lexical Obfuscation A Obfuscated Snippet B Target Code Download Scientific Diagram
2011The concept was originally introduced at the International.

C obfuscation techniques. In addition numerous malicious actions can be performed using an. The code obfuscation is a mechanism for hiding the original algorithm data structures or the logic of the code or to harden or protect the code which is considered as intellectual property of the software writer from the unauthorized. Obfuscation is a technique used to change software code in order to make it harder for a human to understand.
As its name suggests code obfuscation refers to a series of programming techniques designed to disguise elements of a programs code. Cmd c copy powershellexe benignexe File deletion. Its the primary way that programmers can defend their work against unauthorized access or alteration by hackers or intellectual property thieves.
Obfuscation Techniques In general code obfuscation may be applied to source code IL code or final machine code depending on the language used. The best you can do is read the comments of the author of the programs on IOCCC. Discovering CC in Malicious PDFs with obfuscation encoding and other techniques by Filipi Pires - YouTube.
Will always be more obfuscated than result value factor. For example a browser can download a javascript file quicker. Bab Anti ForensicsPembahasan kali ini masih pada teknik anti forensik.
There are several reasons one might obfuscate code. This makes reverse-engineering the distributed code to its original form difficult. Normally it would be applied as part of a build process although for some applications the obfuscated code is incorporated directly into the source code from the start.
In order to have short identifiers obfuscators tend to even define many things. To make it harder for unauthorised parties to copy the code. Invoke-DOSfuscation supports and randomizes all of these obfuscation components File copy.
Reverse Engineering Snapchat Part I. Datacodecomment confusion which includes making some actual code look like comments or confusing syntax with data. Here are a few pointers.
This technique involves moving immediate bytes into a local stack variable to construct a normal C-style null terminated string. Typically more useful for evading static analysis detections rather than dynamic detections. Knowing the preferences of obfuscation techniques can better assist the design of code analysis tools and prioritize the challenges need to be tackled.
Cost-effectiveness is necessary so that an obfuscation technique can be applied on a large scale over several similar applications. There are different techniques to obfuscate these binaries or scripts like build a custom binary disguise them as images using your own crypter or compiling your obfuscated version of the tool. Double coding which can be displaying code in poetry form or interesting shapes.
It is necessary to hide the flow of control of a program. String obfuscation is used by various malware families to prevent important strings from being easily recovered from the executable. The best way to obfuscate the C code is to compile it and distribute only the binaries.
Just include Obfuscationh and obfuscate all the way. Teknik yang digunakan ada dua yaitu lo. This is an obfuscator demonstrating how to use C1114 to generate at compile time obfuscated code without modifying the compiler or using any external obfuscation tools.
Predicting the Resilience of Obfuscated Code Against Symbolic Execution Attacks via Machine Learning Sebastian Banescu Christian Collberg Alexander Pretschner USENIX Security2017. Thomas Rinsma in his Masterss Thesis Seeing through obfuscation. Caret escape character Double quotes evenly balanced Encapsulating parentheses Leading trailing special characters Standard input argument hiding.
On the speci c obfuscation technique in use eg identi er renaming is much less of an issue comparing to string encryption. The numerous software protection techniques have been developed and one of such software protection techniques is code obfuscation. They describe how they manage to obfuscate their code.
To reduce the size of the code in order to improve performance. All roads paving to the correct. Kali ini fokus kita ada pada Trail obfuscation.
2020-06-18 When you have 200 million daily users youll definitely want to keep your API private from spammers and co so youll have to keep a secret in the binary that authorizes it. According to Nick Montfort techniques may include. It obfuscates strings and calls to functions.
The advantage of this. Interactive detection and removal of opaque predicates attacks Tigress opaque predicates. Naming obfuscation which includes naming variables in a meaningless or deceptive way.
Sofware obfuscation transforms computer programs to new versions which are semantically equivalent with the original ones but much harder to understand Collberg et al. In the second approach the data obfuscation techniques are applied on-the-fly to execute and control the data by the system. Cmd c del benignexe.
CC machine code output after decompilation is itself obfuscated hence it involves a level of obfuscation built-in. Based on the ADVobfuscator. The layered obfuscation techniques that follow should serve as compelling evidence that many obfuscation techniques are never removed from child process arguments.
1997It is a technique which protects software intellectual properties against MATE Man-At-The-End attacks Collberg et al. Obfuscating C C and C.
Pdf Assessment Of Source Code Obfuscation Techniques Semantic Scholar

Top 7 Source Code Obfuscation Strategies

Obfuscation Code An Overview Sciencedirect Topics

Examples Of Control Flow Obfuscation A Original Rtl Cdfg B Download Scientific Diagram

Possible Ways Of Obfuscating Parameters To Calls Download Scientific Diagram
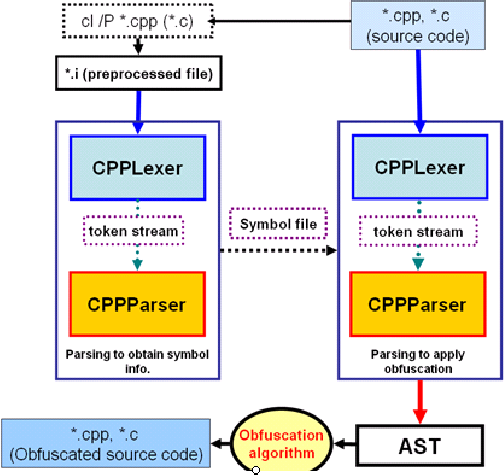
Pdf Implementation Of An Obfuscation Tool For C C Source Code Protection On The Xscale Architecture Semantic Scholar

Pdf Code Obfuscation For The C C Language Semantic Scholar
Obfuscation Techniques Left To Right A Original Plain Image B Download Scientific Diagram

What Is Obfuscation Preemptive

Obfuscated Example Snippet Download Scientific Diagram
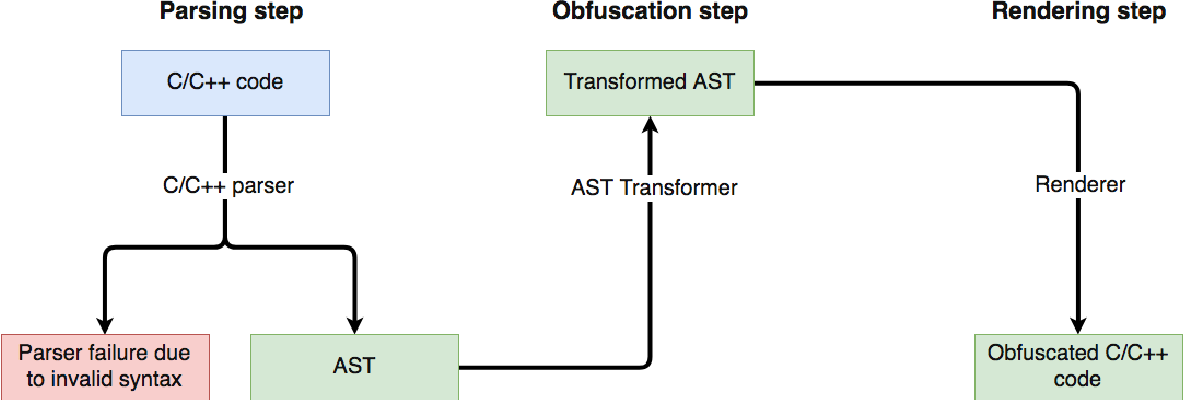
Pdf Code Obfuscation For The C C Language Semantic Scholar

What Is Obfuscation Preemptive

Overcoming The Obfuscation Of Java Programs By Identifier Renaming Semantic Scholar
Posting Komentar untuk "C Obfuscation Techniques"